VPN scams: How to spot fake VPNs and stay safe
As virtual private networks (VPNs) become more widespread, misleading services and deceptive marketing have also emerged to take advantage of this demand. Some apps marketed as VPNs have been found to contain malware or other unwanted functionality. Others may function as VPNs but still mislead users through unclear billing practices, fake reviews, or vague logging and data-sharing disclosures.
This article explains the main ways scammers exploit the popularity of VPNs, the risks these schemes pose, and how to recognize the warning signs of a disreputable service.
What are VPN scams?
The term “VPN scams” encompasses several deceptive practices, including fake VPN apps, dishonest providers, and misleading campaigns that exploit the popularity of VPN services.
One of the clearest examples is malware disguised as a VPN app or installer. For example, in March 2026, Microsoft reported that attackers used spoofed VPN sites and fake clients to harvest credentials.
Not every service described as a “VPN scam” is necessarily breaking the law in the same way. For example, a provider that collects user data may not be acting illegally if its practices are clearly disclosed and otherwise comply with applicable law. But providers that misrepresent their logging, privacy, or security practices can face legal risks, including enforcement by the Federal Trade Commission (FTC) for deceptive or unfair acts or practices.
Exaggerated marketing claims and misleading reviews are another concern. Some services may make false claims about privacy and security standards. Even if a provider does not intend to mislead users, an insecure VPN infrastructure can pose risks to users’ privacy and security.
Why scammers target VPN users
Concern about tracking, data collection, and online surveillance leads many people to seek out VPNs, which are widely associated with privacy and security. That makes them an attractive lure for scams that imitate trusted VPN brands or services.
At the same time, many VPN shoppers may be comparing unfamiliar claims about encryption, logging, and infrastructure. That can make it harder to distinguish a reputable provider from a misleading one.
How VPN scams put you at risk
Please note: These risks are typically associated with poorly implemented or deceptive services, rather than well-established VPN providers with transparent practices.
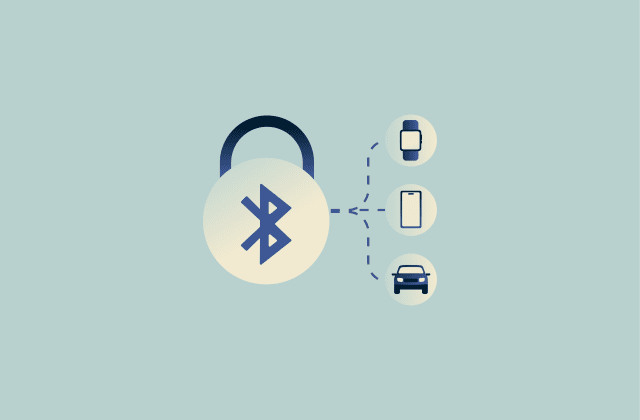
A VPN encrypts traffic between a device and the VPN server, helping protect data from interception along the network path. This is the main benefit of using one, but it also means users are relying on the VPN provider to handle their data responsibly.
Depending on the service design and the use of HTTPS or other end-to-end encryption (E2EE), a less transparent or poorly secured provider may still be able to observe some connection metadata (such as timestamps or IP-related information).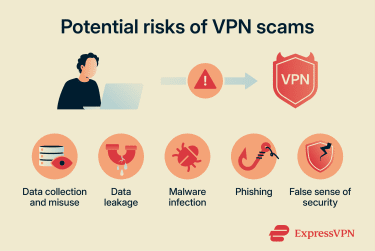
VPN scams are diverse, but the potential harm is generally confined to a few key areas. The major risks are:
- Data collection and misuse: Some VPN providers may collect more technical, device, connection, or usage-related data than users expect and may share it in ways that are poorly disclosed.
- Data leakage: In some cases, poorly implemented VPNs can leak traffic through Domain Name System (DNS), IPv6, or Web Real-Time Communication (WebRTC), exposing browsing activity outside the VPN tunnel.
- Malware infection: Some fake VPN apps are actually malware and may spy on users, steal credentials, or compromise devices.
- Phishing: Scammers may imitate VPN providers and direct targets to fraudulent login or download pages meant to steal credentials.
- False sense of security: Misleading privacy claims, poor security practices, or excessive logging can lead users to believe they are safer than they actually are.
Common VPN scams to watch for
VPN scams don't follow a single pattern. To stay safe, it helps to understand the main ways scammers exploit VPN users.
Fake VPN apps and look-alike websites
Scammers can create fake VPN apps to deliver a range of threats. Some are designed to steal credentials, install malware, take over devices, commit banking fraud, or inject ads. Some may appear to work as VPNs while delivering the malicious payload, while others may not function at all.
Attackers can imitate well-known VPN applications and distribute them through malicious websites, and in rare cases, they may appear on app marketplaces before being removed. The software may mirror the branding, interface design, and naming of legitimate products, making it difficult to distinguish from authentic versions at first glance. In other cases, scammers may use original branding for their fake VPN, but the dangers are much the same.
Some attackers and organized groups may use search engine optimization (SEO) poisoning to push fake VPNs up search results. Another common tactic is the use of lookalike domains. For example, a cybercriminal may register a website with an address that closely resembles a widely used VPN. Believing they are interacting with a legitimate service, visitors may be prompted to download installers or enter login credentials.
Free VPN services and privacy trade-offs
Free VPN services can be particularly appealing, especially for those who’ve never used one. Being free does not make a VPN a scam, but some free services rely on business models that can undermine privacy.
Operating a VPN requires infrastructure, bandwidth, and ongoing maintenance. Providers without subscription revenue may generate income in ways that are not conducive to privacy. Common methods include:
- Advertising or ad-supported monetization: The service may rely on ads or other monetization methods that create incentives to collect more data than users expect.
- Excessive data collection or sharing: The VPN may collect browsing-related, device, connection, or account data and share it with third parties such as analytics, advertising, or service providers
- Bandwidth resale or proxy-network use: The VPN may use customers' idle connections or IP addresses as proxy nodes within third-party networks.
Though these practices aren’t ideal for consumers, a service that relies on any of them isn't necessarily fraudulent. But some free VPN scams may actively mislead users about how data is handled or how the service works.
Too-good-to-be-true lifetime deals
Some VPN providers advertise lifetime subscriptions that promise unlimited access for a single payment.
These offers may appear attractive, but maintaining VPN infrastructure requires continuous investment in servers, bandwidth, development, and security. That can make the long-term sustainability of one-time-payment plans harder to assess.
There’s no guarantee that the service will maintain operations in the long run. There have been instances of online services, including VPN providers, discontinuing lifetime subscriptions or shutting down. In general, users should be cautious about this subscription model.
Fake reviews, awards, and endorsements
Online reviews can influence many purchasing decisions. Unfortunately, deceptive review and endorsement practices can make it harder to evaluate VPN services.
Some providers and comparison sites may promote services through paid partnerships or affiliate relationships. When these relationships are not clearly disclosed, or when rankings and reviews are presented as independent despite financial incentives, it can make it harder for users to assess the credibility of the recommendations.
Trustworthy review sites and providers clearly disclose sponsorships, explain how rankings are determined, and distinguish between editorial content and paid promotion.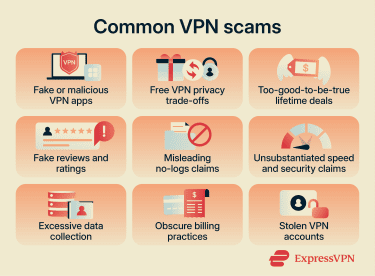
Misleading no-logs claims and hidden data logging
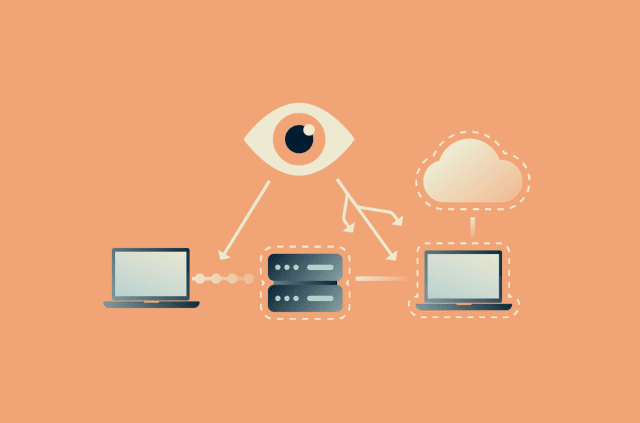
Many VPN providers advertise no-logs policies, generally meaning the service doesn’t store information about user activity.
However, not all no-logs claims are defined or implemented in the same way. VPN services may still need to process some account, billing, technical, or connection-related data to operate. The important factors are the types of data collected, how long they are retained, and whether those practices match the provider’s claims.
At one end of the spectrum, a provider may collect extensive activity or usage data. Less invasively but still potentially concerning, some services may keep connection metadata such as timestamps, device identifiers, or IP-related information. Whether this affects user privacy depends on the scope and handling of that data.
Because of these differences, it’s important to look closely at the no-logs policy. Trustworthy VPN providers clearly define what they do and do not log, and they typically back up their claims with independent audits.
A no-logs policy can be a meaningful privacy feature, but only when it’s specific, transparent, and consistently implemented. Vague or inconsistent claims can be a red flag.
Unsubstantiated speed and security claims
Marketing materials frequently emphasize encryption strength and connection speed. Without a technical explanation, generic statements offer little insight into the service's actual security. Providers that clearly explain their protocols, encryption, and leak-protection features are generally easier to evaluate than those that rely solely on vague claims.
Speed is also influenced by many factors, including server location, network conditions, device performance, and the protocol in use. More reliable providers typically explain how their network is designed to optimize performance, rather than relying on absolute or universal claims.
Legitimate VPN providers typically disclose the technical mechanisms behind their operations. On the other hand, exaggerated claims without substance may indicate an untrustworthy provider.
VPNs that request extensive personal information
Many VPN services require limited information during account creation, often an email address and payment method, though the exact requirements vary by provider and payment option.
Requests for additional personal data, such as a phone number or identity documents, may indicate more extensive data collection. Some information, such as billing details, may be required, but it is worth being cautious if a service asks for substantially more information than is normally needed to create an account or process a payment. The FTC also advises users to review VPN app permissions, terms, and privacy policies carefully.
Collecting unnecessary information increases the potential impact of a breach and raises the risk of identity theft if databases are compromised. It’s also possible that scammers might create a fake VPN site solely to collect data from newly registered “users.”
That said, some jurisdictions have introduced or proposed age-verification rules for access to certain online services. Where those rules apply, users may be asked for additional information by the platform or a third-party verification provider.
Subscription and billing pitfalls
Some VPN services use subscription, renewal, or refund structures that are unclear or hard to navigate. While these practices aren’t inherently illegal, confusing terms or difficult cancellation processes may sometimes be exploited by bad actors to create subscription traps or make refunds harder to obtain.
Common issues to watch for include unclear renewal terms, limited refund windows, opaque billing, and complex cancellation processes.
Cracked and stolen VPN accounts
Other scammers aim to provide illicit access to otherwise reputable VPN providers. This is often accomplished by stealing the login credentials of legitimate customers and reselling that access.
Offers on forums or unofficial marketplaces advertising free or heavily discounted VPN access should be treated with suspicion. Using compromised accounts can lead to account suspension and help sustain broader credential-theft networks.
How to spot a VPN scam before you install
Several indicators can help distinguish trustworthy providers from questionable services. Looking for these signs can reduce the risk of installing a misleading or unsafe VPN.
Always verify the official website and app source; fake or lookalike domains are a common tactic used by scammers to distribute malware or harvest credentials. Some signs may be visible on an app store page or website, while others may require checking the provider’s privacy policy or technical documentation.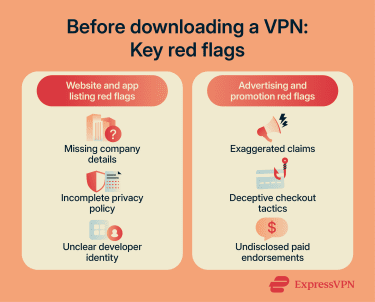
Signs of an unreliable VPN service
There are often telltale signs that a VPN service is suspicious. Though none of these signs necessarily means that a VPN is engaged in illegal activity, they may indicate that it's less reputable than others. Red flags on a VPN provider’s website or app store listing include:
- Missing company information: More transparent providers usually identify the organization that operates the service and provide verifiable company or contact details.
- Incomplete privacy policy: A vague or incomplete privacy policy can make it harder to assess what data is collected, retained, or shared with third parties.
- Unknown developer identity: App listings without a clear developer identity or track record may signal higher risk.
General differences can also be drawn between how legitimate and less reputable VPNs present themselves. Marketing materials and product descriptions for less reputable providers are more likely to include:
- Extreme claims: Promotions promising total anonymity or unlimited speed without explanation.
- Manipulative tactics: Offers that create urgency without clearly explaining pricing, renewal terms, or conditions.
- Unverified endorsements: Promotions or testimonials that don't clearly explain sponsorships, affiliations, or how the recommendation was made.
Verify reviews and ratings
Evaluating reviews across multiple sources can sometimes reveal patterns that suggest manipulation. Balanced reviews usually mention both strengths and limitations of a service. Identical wording across many testimonials or sudden bursts of positive ratings may indicate coordinated promotional campaigns rather than genuine feedback.
Check who runs the VPN
Transparency about ownership is an important indicator of trustworthiness. More transparent VPN providers usually publish information about the company operating the service, such as ownership details, headquarters location, or other verifiable company information. A lack of verifiable information about the organization behind a VPN can be a red flag.
Read the VPN privacy policy
A VPN privacy policy explains how user data is collected, stored, and processed.
Important elements include the types of information collected, how long that data is retained, and whether it’s shared with third parties. Policies that clearly describe these practices demonstrate stronger transparency.
Rather than simply trusting a claim that no user data is logged, it’s better to check how specific categories of data are handled. If a policy doesn't clearly explain whether it collects or retains IP-related activity or DNS-related data, that can be a red flag.
Look for key encryption and security features
Reliable VPN security depends on modern encryption standards, secure tunneling protocols, and leak-protection mechanisms that prevent the accidental exposure of user data. When evaluating a VPN, look for clear information about the encryption standards it uses (such as Advanced Encryption Standard (AES)-256), the tunneling protocols it supports (such as Lightway, OpenVPN, or WireGuard), and whether the service includes protections against DNS, IP, and WebRTC leaks.
Clear documentation of these technologies is a good sign. Less reputable services are more likely to rely on vague claims rather than specify protocols or security features.
How to choose a legitimate VPN
After screening for red flags, it helps to look for signs of a well-run service:
- Secure apps and vulnerability response: Reliable providers maintain apps across major platforms, release security updates, and may offer a vulnerability disclosure or bug bounty program.
- Independent audits: Look for audit information that explains what was reviewed, who conducted it, and whether the assessor was independent.
- Clear ownership and support: Trustworthy providers usually identify the company behind the service and offer clear documentation and accessible support channels.
Some VPN providers publish details about their security architecture, data-handling practices, and independent audits in dedicated transparency resources. The ExpressVPN Trust Center outlines how its service is built and independently reviewed, providing detailed accountability resources to demonstrate how it protects users’ privacy.
FAQ: Common questions about VPN scams
Are VPNs scams?
How do you know if a VPN is legit?
Are free VPNs scams?
Do VPNs steal your information?
Is using a VPN illegal in the U.S.?
Is there a reason not to use a VPN?
What should you do if you fall victim to a VPN scam?
How can users protect their personal information while using a VPN?
Which VPNs are considered safe?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN