Strong VPN encryption and security explained
VPN encryption is complex, relying on well-tested implementation of advanced mathematics. Read on to learn how ExpressVPN uses strong encryption to keep your data and communications safe.
Video: How VPNs use tunneling and encryption
How secure is ExpressVPN encryption?
Besides hiding your IP address and mixing your traffic with that of other users, ExpressVPN also encrypts your traffic between secure VPN servers and your computer. This keeps your data safe from being read by third parties.
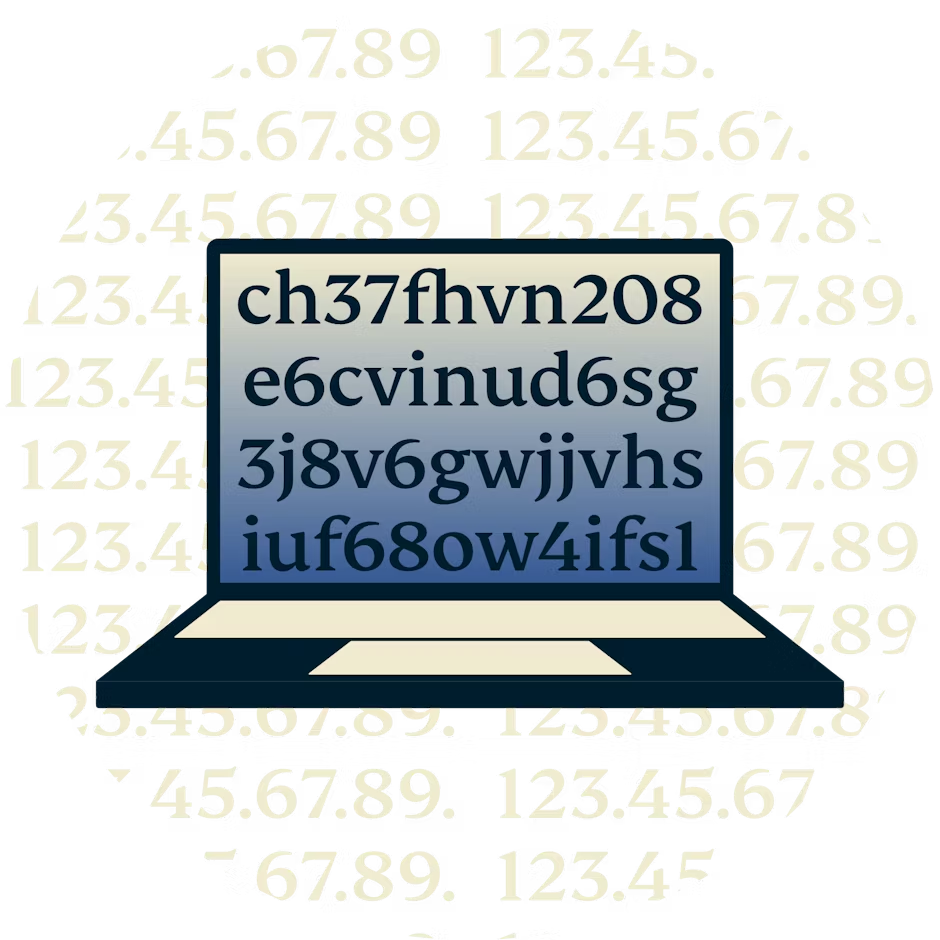
ExpressVPN uses AES (Advanced Encryption Standard) with 256-bit keys—also known as AES-256. It’s the same encryption standard adopted by the U.S. government and trusted by security experts worldwide to protect classified information.
256-bit keys means 2^256 or 1.1 x 10^77 possible combinations. That’s 115,792,089,237,316,195,423,570,985,008,687,907,853,269,984,665,640,560,000,000,000,000,000,000,000,000 combinations! A brute-force attack on a 256-bit keyspace is simply infeasible, even if all the world’s most powerful supercomputers ran for as long as the universe has existed so far, billions and billions of times over.
VPN protocols: Lightway
ExpressVPN offers a variety of VPN protocols to implement strong and safe encryption between your computer and the VPN server location you connect to. When you use the ExpressVPN app, you can easily switch between the protocols, although it’s recommended that you choose the automatic setting, which will select the protocol optimal for your speed and security.
In addition to offering a standard set of protocols, including OpenVPN and IKEv2, ExpressVPN built Lightway to outdo them all in speed, reliability, and security. Give it a try to see for yourself. Learn more about Lightway.
Here are some of the features of ExpressVPN encryption with Lightway:
Server authentication
Like HTTPS and OpenVPN, Lightway uses certificates to protect the user against man-in-the-middle attacks. Your VPN client has a certificate preloaded that is used to authenticate a VPN server.When using an external or open-source Lightway client, you will be able to load this certificate yourself to connect with VPN servers.
The two ciphers used in Lightway are AES-256-GCM and ChaCha20/Poly1305. Owing to the excellent hardware acceleration of AES available in most devices, Lightway will mostly default to this well-proven cipher. Only on lower-powered routers or entry-level mobile devices might ChaCha20 be used.
HMAC authentication
HMAC stands for keyed-Hash Message Authentication Code. This code protects the data from being altered in transit by an attacker who has the ability to read the data in real time. TLS and OpenVPN also use hashes for authentication, hence the H in HMAC.
Control-channel encryption
To ensure the integrity and confidentiality of encrypted data even on low-powered hardware, ExpressVPN uses AES-256-GCM. AES is one of the most widely used symmetric encryption standards. The 256 refers to the fixed size of each encrypted block, 256 bits. GCM (Galois/Counter Mode) allows your computer to encrypt multiple packages at once, ensuring that your connection never hangs even for a short moment.
Data-channel encryption
Data-channel encryption protects against your information being visible to the parties that your data travels through. ExpressVPN uses a symmetric encryption scheme, in which the key is negotiated using the elliptic curve Diffie-Hellman key exchange. The ExpressVPN server and your VPN app use clever mathematics to negotiate and verify a secret key that is then used to encrypt the data for the entire session.
Post-quantum protection
By integrating post-quantum support with DTLS 1.3, we are fortifying our VPN service to remain secure in the face of quantum computing advancements.
Lightway includes post-quantum protection by default, shielding you against attackers with access to both classical and quantum computers. ExpressVPN is one of the earliest VPNs to deploy post-quantum support, future-proofing our users for a quantum-safe world.
Download ExpressVPN on all your devices
A single ExpressVPN subscription lets you download a VPN for every popular platform. Need a VPN for multiple devices? Set up ExpressVPN on everything you own, and use it on eight at the same time.

Frequently asked questions
Can ExpressVPN be trusted?
As a privacy-focused company, ExpressVPN has worked tirelessly to earn the trust of both our customers and the industry, even working with the Center for Democracy and Technology to develop a set of standards that VPN services should be able to demonstrate to signal their trustworthiness.
We’ve also developed industry-leading security initiatives like:
- TrustedServer, an independently audited VPN server technology that delivers unparalleled privacy protections; and
- Lightway, a custom-built VPN protocol that’s faster, more reliable, and more secure than standard protocols. We have open sourced its core code for full transparency.
How do I know ExpressVPN is secure?
Security is at the forefront of what we do at ExpressVPN. Not only do we aim to design our apps and systems to offer a high level of privacy and security, but we also routinely engage independent auditors to validate our security claims. It’s one of the best ways for our users to know if they can trust our services to protect them. See the full list of audits and read the full reports.
Is ExpressVPN safe and legal?
Yes. ExpressVPN provides a valuable layer of security to your online experience, especially on public Wi-Fi networks. This helps to ensure safe access on any network.
Further, VPNs are legal in the vast majority of jurisdictions around the world and are widely used by individuals and companies to protect their data. Even in regions where use of a VPN may be discouraged, many governments tacitly endorse their use by officials, academics, or businesses to stay competitive in an interconnected world. It is simply not practical for countries to ban all VPNs.
Having said that, illegal online activity is always illegal, whether you are using a VPN or not.
Can ExpressVPN be hacked?
ExpressVPN takes your privacy extremely seriously and takes full measures to ensure the security of our service. ExpressVPN does not collect users’ connection or traffic logs, plus our proprietary TrustedServer technology ensures all data is wiped from servers with every reboot. Read more about our methods of making systems difficult to compromise and minimizing potential damages if a compromise does occur.
Meanwhile, using a VPN protects you from hacking methods such as packet sniffing and man-in-the-middle attacks. In fact, using a VPN is good practice for every type of connection, but it can be particularly useful when browsing unsecured HTTP websites. Expats, travelers, and all kinds of on-the-go individuals should use a VPN whenever they’re on an untrusted network like free public Wi-Fi.
Is ExpressVPN really private?
ExpressVPN greatly enhances your privacy by encrypting your online traffic and giving you a different IP address. This means less monitoring and tracking by third parties. We also never keep logs of your online browsing activity. Even if law enforcement were able to compel us to provide user data, we can’t provide data we don’t have.
Does ExpressVPN sell your information?
No. ExpressVPN is first and foremost a privacy company and therefore stores no activity logs and no connection logs. ExpressVPN also never stores any data that would allow anyone to trace a specific network activity or behavior back to an individual user. This means that there is no information to sell.
ExpressVPN only collects and uses personal information for the purposes listed in our Privacy Policy, and we do not sell your personal information to third parties .
Learn more about using a VPN
-
![A laptop's secure connection to the internet.]()
-
![A plant at his laptop using ExpressVPN.]()
-
![Laptop with several browser windows.]()
Unblock websites
Access your favorite web services and defeat censorship
Security and privacy
Ready to try the best encrypted VPN?
VPN encryption is essential. Give ExpressVPN a try. You’re 100% covered by our 30-day money-back guarantee.