Expressvpn Glossary
Information security management system (ISMS)
What is an information security management system (ISMS)?
An information security management system (ISMS) is a structured framework that organizations use to manage and reduce information security risks.
It consolidates security requirements into a consistent set of policies, processes, and controls that help protect information systematically rather than through ad hoc or departmental responses.
An ISMS supports the confidentiality, integrity, and availability of information. In practice, this means helping keep data private, accurate, and complete, and accessible when needed.
How does an ISMS work?
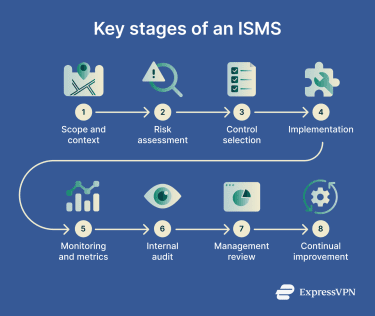
An ISMS operates as a continuous, organization-wide process for identifying, managing, and reducing information security risks. It is established within a defined scope and maintained through ongoing review and improvement. It typically includes the following stages:
- Scope and security objectives: An organization determines which information, systems, and processes the ISMS covers and defines what the security program aims to achieve, such as protecting customer data or meeting regulatory requirements.
- Asset identification and ownership: Important information assets are cataloged, and responsibility for them is assigned to specific individuals or teams to help secure appropriate protection and oversight.
- Risk assessment: Security teams evaluate potential threats and vulnerabilities based on their likelihood and impact, then select controls such as encryption, access restrictions, or monitoring tools to treat the identified risks.
- Policy implementation and training: The organization formalizes security requirements into enforceable policies that can be translated into day-to-day procedures. Employee awareness programs and role-specific training are critical for the consistent application of these controls.
- Monitoring, auditing, and improvement: The effectiveness of controls is tracked through security metrics, reviewed through internal audits, and updated in response to emerging threats, incidents, or changes in the business environment. External audits may also apply for certification or regulatory purposes.
Why is an ISMS important?
An ISMS helps organizations manage information security proactively rather than reactively. By identifying risks early and applying appropriate controls, organizations can reduce the likelihood and potential impact of security incidents.
Beyond reducing risk, an ISMS improves governance and accountability. Defined roles, documented processes, and regular reviews help organizations show stakeholders, regulators, and customers how sensitive information is protected.
Lastly, an ISMS helps organizations meet legal, regulatory, and contractual security requirements through documented controls that can be reviewed during audits.
Where is an ISMS used?
An ISMS can be used by organizations of any size and in any sector, but it is especially common in organizations that handle sensitive or confidential information and require a consistent risk management approach.
For example, Software-as-a-Service (SaaS) providers and digital service companies use an ISMS to help protect customer and application data, while regulated sectors such as healthcare, finance, and critical infrastructure often rely on structured security management to support compliance and risk reduction.
Government agencies, contractors, and organizations pursuing International Organization for Standardization (ISO) / International Electrotechnical Commission (IEC) 27001 certification also commonly implement an ISMS as part of their security strategy. Smaller companies may adopt a scaled ISMS based on their risk profile, business needs, or customer and contractual requirements.
Risks and privacy concerns
Somewhat counterintuitively, an ISMS can introduce security risks if poorly implemented. One common issue is a “paper ISMS,” where policies exist but aren't supported by effective controls, enforcement, or ongoing review.
An overly broad ISMS scope can also create problems. Organizations that include too many systems and processes before they have mature controls and governance in place may struggle to apply controls consistently, maintain evidence, and manage risks effectively across the full scope.
Other common weaknesses include inadequate risk assessments that miss critical threats, poor oversight of third-party vendors, and misconfigured access controls. These gaps can increase exposure even when policies appear comprehensive on paper.
Further reading
- Why software security audits matter
- Security concerns in cloud computing
- What is cybersecurity?
- Cybersecurity tips for small businesses
- What is zero-trust architecture?

